Ethical Hacking: Trojans And Backdoors Lisa | Bock Videos
Let’s walk through the key takeaways. A Trojan horse is malicious software disguised as legitimate software . Unlike viruses or worms, Trojans do not replicate themselves. They rely entirely on social engineering—tricking you into clicking, installing, or opening something.
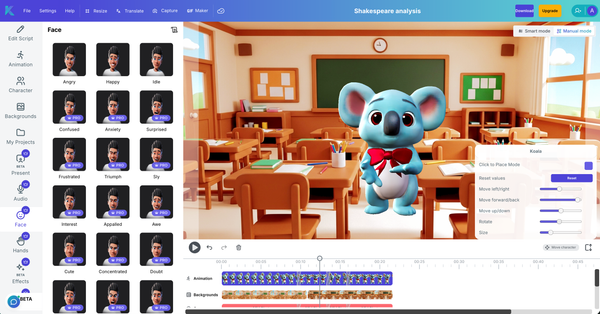
In her excellent video series on ethical hacking, (a renowned author and cyber security instructor) breaks down how Trojans and backdoors remain two of the most dangerous tools in a hacker’s arsenal—and why every security professional needs to understand them. ethical hacking: trojans and backdoors lisa bock videos
By: Security Learner Inspired by the ethical hacking teachings of Lisa Bock Let’s walk through the key takeaways
on LinkedIn Learning for deep dives into packet analysis, reverse engineering, and the specific commands used to detect RATs running in memory. Have you ever encountered a suspicious email attachment? Share your experience in the comments below. They rely entirely on social engineering—tricking you into